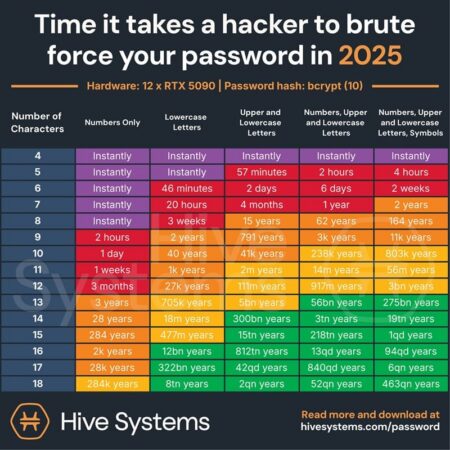
The Hive Systems 2025 Password Table Shows How Quickly Your Passwords Can Be Cracked
In an age of rapid technological advancements, one thing is certain: what was secure yesterday can already be a vulnerability today. This is exactly what Hive Systems’ new 2025 Password Crackability Table demonstrates. It impressively reveals just how quickly or alarmingly quickly attackers can crack passwords. The basis for this: real-world hashing standards, current GPU hardware, and the latest attack strategies from the field. But what does this mean specifically for your company and for you personally?
Computing power trumps habit

- The central message of the table is clear: the shorter and weaker a password, the faster it is compromised. But it’s not just the length of a password that matters—it’s also how it’s stored. This involves a kind of “secret code” (called “hashing”) that makes the password unreadable. The better this code, the harder the password is to crack.
- In the past, passwords were often secured using simple methods like “MD5.” This is a process that converts a password into a numerical code but this code is easy to crack today and is considered insecure. Today, modern systems increasingly rely on bcrypt, an algorithmic security layer that deliberately “slows down” passwords through numerous computational operations thus making them harder to crack. In its analysis, Hive Systems based its findings on a security standard frequently used in practice: a so-called “10-fold protection level” using bcrypt 10 technology. This roughly corresponds to what many well-known software systems automatically employ when storing passwords.
- At the same time, computing power was massively increased: Instead of working with just a single graphics card as before, this time an entire “computing turbo” was deployed a cluster of twelve extremely powerful RTX 5090 graphics cards. In other words, the best currently available on the consumer market. And that makes a difference. You can imagine it as twelve supercars working together to complete a task that used to be handled by a single compact car. And that makes a huge difference in speed.
What’s the technical background?
The table analyzes how long it takes to crack a password depending on its length, complexity (upper- and lowercase letters, numbers, symbols), and the hash function used.
An example:
- An 8-character password consisting only of lowercase letters can be cracked in under a second.
- With a full range of characters (upper- and lowercase letters, numbers, special characters), a 12-character password would take centuries provided bcrypt is used correctly.
- However, as soon as passwords appear in data breaches or are easy to guess (“Hello123!”, “Spring2024”), even supposedly secure variants shrink to fractions of a second.
Hive Systems also factors in dictionary attacks, leaks from the dark web, and machine-based pattern matching into its calculations. This provides a realistic picture of how “secure” a password actually is in the real world and not just under lab conditions.
Why this matters to everyone including your company
Cyberattacks aren’t just getting faster they’re also getting cheaper. The computing power that used to be available only to government actors or large corporations is now accessible to small hacker groups or even individuals. Cloud services like AWS or Azure offer GPU clusters on an hourly basis a nightmare for weak passwords and outdated hashing methods.
For companies, this means:
- Employees with weak passwords not only put their own accounts at risk, but often the entire network as well.
- If passwords are poorly protected, the customer database quickly becomes a risk. A single attack can then cause significant damage. Poorly hashed databases turn attacks on customer databases into a ticking time bomb.
- Compliance requirements (e.g., GDPR, ISO 27001) have long demanded modern security measures including for password storage.
Recommendations for Action – Take Action Now
To ensure your passwords remain in the “green zone,” Hive Systems recommends and we strongly endorse the following measures:
- Use strong passwords: At least 12 characters, randomly generated, with uppercase and lowercase letters, numbers, and symbols.
- Avoid reusing passwords: Each system should have its own password use a password manager for this.
- Store passwords as if you were keeping them in a steel safe not in a cardboard box. Use secure methods such as bcrypt, Argon2, or scrypt.
Outdated methods like MD5 or SHA1 are easy to crack they offer virtually no protection. - Supplement your logins with two-factor authentication (2FA): Even if a password is compromised, a second factor reliably protects against unauthorized access. One of the most effective and user-friendly options is 2FA via SMS. With this method, the user receives a one-time code via SMS that must be entered in addition to the password simple, fast, and compatible with virtually any device.
- Raise awareness among your team: Security starts with behavior. Provide regular training on topics such as password hygiene, phishing, and social engineering
Conclusion: Password security is a process not a static state
The new password chart from Hive Systems is more than just a pretty picture. It’s a wake-up call. Anyone who thinks they’re safe with “password123” or “sunshine!” is dangerously mistaken.
In Switzerland, too, we’re seeing a sharp rise in phishing attacks, ransomware, and credential stuffing. The first line of defense against all of this? A secure, well-hashed, unique password combined with modern security standards. Stay in the green zone for yourself, your company, and your customers.
Link to the original table from Hive Systems: Are your passwords in the green?
Would you like to better protect your business against password threats? We’d be happy to advise you on 2FA via SMS, security notifications, and secure authentication workflows with eCall Business Messaging.

Florian
Florian Frei is Senior Marketing Manager at F24 Schweiz AG and responsible for the positioning of the eCall Business Messaging brand. In his articles, he writes about professional business messaging, omnichannel communication, SMS, WhatsApp Business, two-factor authentication, data protection and digital customer communication for companies.
Source of article image: www.hivesystems.com/password